新型REvil勒索软件死灰复燃

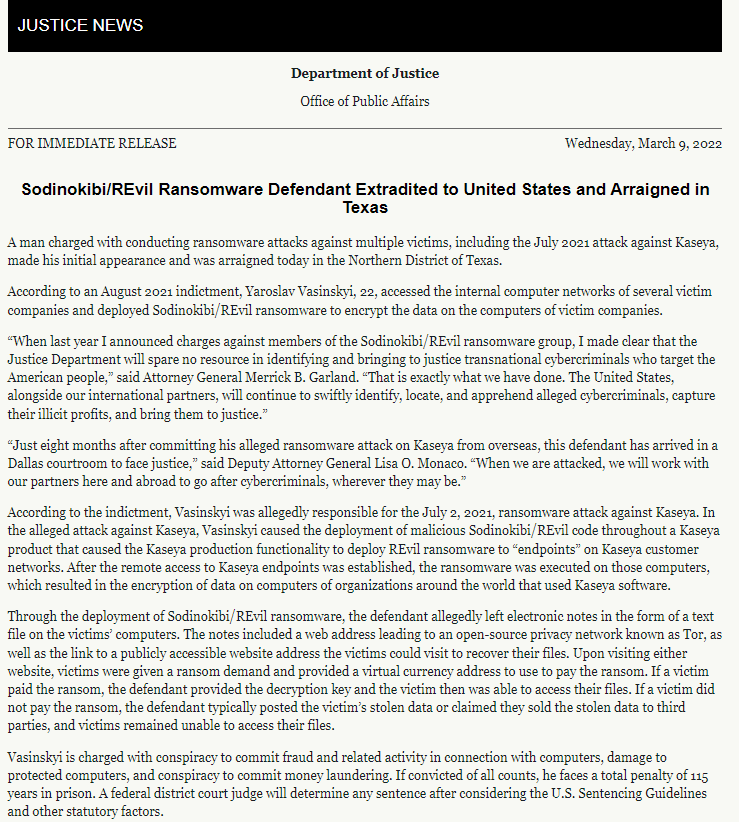
奇安信威胁情报中心从2019年起就一直在跟踪REvil/Sodinokibi勒索软件及其背后的运营商,处理了多起与其相关的勒索事件。直到2021年十月份,据相关媒体报道美国FBI联合其他部门控制了REvil的部分基础设施,并在11月份指控了两名投递REvil勒索软件的人员。2022年1月俄罗斯FSB称在美国提供的相关信息后他们彻底毁灭了REvil并抓捕了几名人员[1]。

事件概述
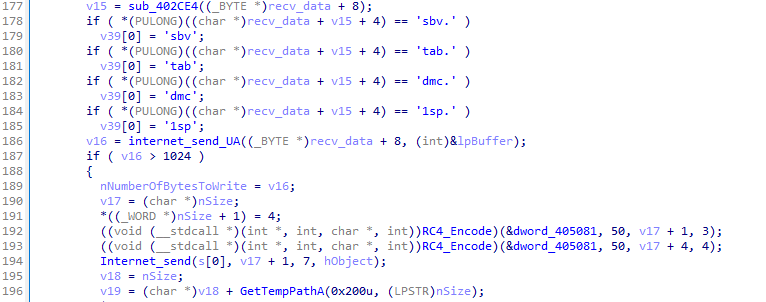
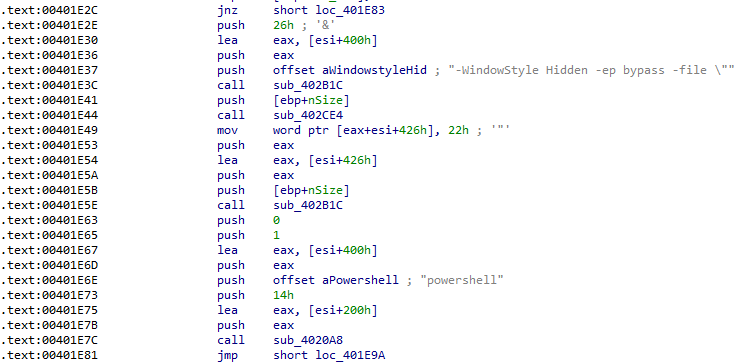
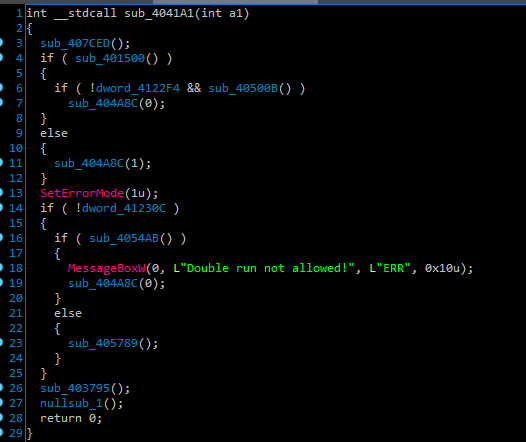
我们观察到一股未知团伙正在利用受Log4j影响的VMware漏洞在内网中进行漫游,使用GO Simple Tunnel工具建立隧道,使用Psexec尝试投递SystemBC 轻量级后门。
SystemBC最早被发现于2019年,被用于各类犯罪团伙,目前与Ryuk、Egregor、DarkSide等勒索软件的投递有关,SystemBC除了正常的TCP连接外,还能通过Tor网络进行连接,考虑到网络等因素本次发现的SystemBC Tor配置信息为空,取而代之是两个用于TCP连接的C2:
46.30.188.222:4210
185.228.83.69:4210
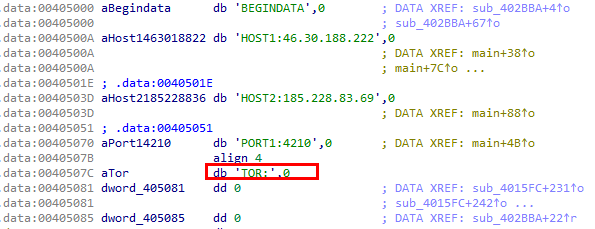
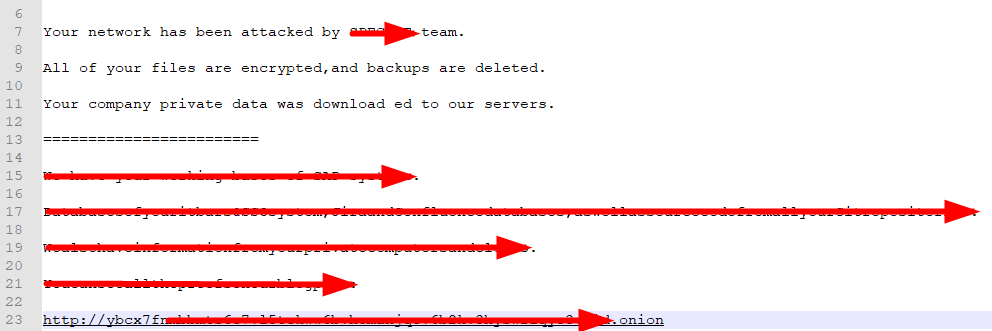
ybcx7fnm********************************.onion
*******_support@protonmail.com
溯源分析
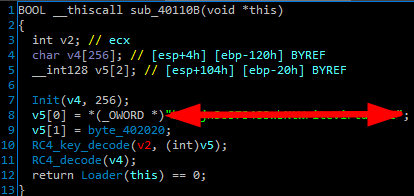
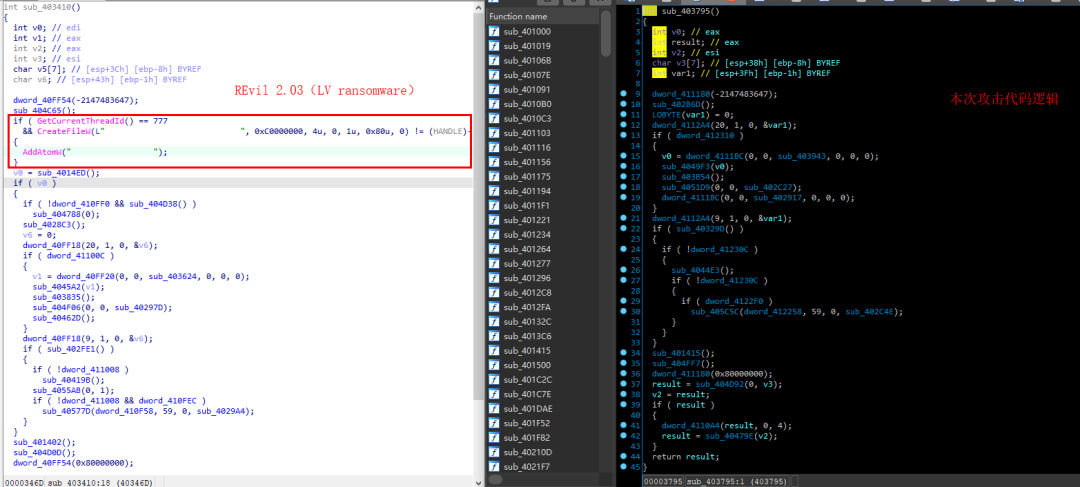
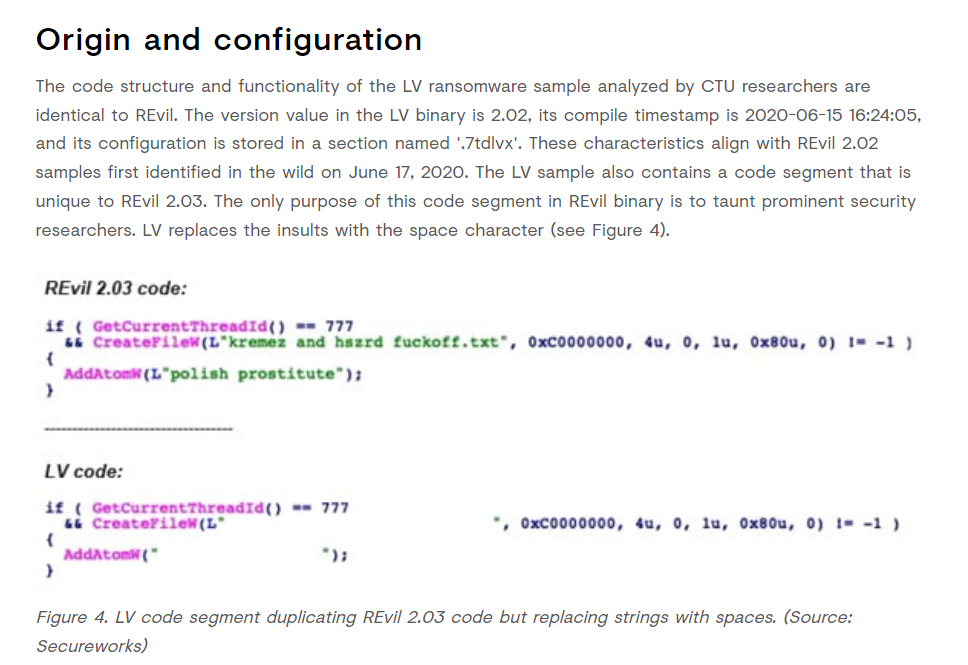
通过仔细对比我们发现,唯一改动的地方就是本次攻击者将Revil源码中原本用于嘲讽受害者的代码进行了删除
总结
目前,基于奇安信威胁情报中心的威胁情报数据的全线产品,包括奇安信威胁情报平台(TIP)、天擎、天眼高级威胁检测系统、奇安信NGSOC、奇安信态势感知等,都已经支持对此类攻击的精确检测。
SystemBC
fa32fe9cf951fc0c9e15b84cdc8f1e8a
ce4f5903bb3109933416b7aa6e6531fb
ac1791ef68b958549da57a51ec7f1811
1224e7cc00eaf62391399cefdd22884b
43c63bf03cff27a4696d80b290eddd19
df8fd5e415ba533bd468e132dda4e0a6
80f563f3992e9e7d87086f3f4966969f
73654c88ec4c3d3e30153e93a5b18dcb
8975fec2a8036303acd074cb7aacdf31
065508fb4e0db0d6101f3be670dbe39a
a3eb2f3b7e15f64a6fd7d5aaba1a84c0
b54a0b8ea3c6ab313ce7ee4dc1128fd9
af1a1fa898e3e42bea3e05809be20882
a830969d630c15b26ecf4d3f65c1ba11
70.34.251.143:4224
46.30.188.222:4210
185.228.83.69:4210
88.80.188.245:4170
93.115.29.50:443
192.53.123.202:443
192.53.123.202:4127
5.101.78.2:4127
212.114.52.115:4208
195.2.73.44:4001
62.113.255.11:4210
193.29.56.71:4210
173.255.208.126:4170
192.169.6.197:4210
5.183.95.197:4210
162.33.179.20:4001
192.53.123.202:4001
46.166.161.93:443
参考链接
[1] https://www.bbc.com/news/technology-59998925
[2] https://www.justice.gov/opa/pr/sodinokibirevil-ransomware-defendant-extradited-united-states-and-arraigned-texas
[3] https://www.secureworks.com/research/lv-ransomware